Responder - Windows
- justinblawitz
- Oct 8, 2025
- 3 min read
Ping and Nmap the target Ip using nmap -p- --min-rate 1000 -sV {target Ip}

We find port 80/tcp open running an Apache web server, and port 5985/tcp open running WinRM (Windows remote management)
Next, we’ll enter the target Ip into a browser to try and reach the web page. We can’t access it but in the search bar we were redirected to http://unika.htb which our host doesn’t know how to find. This is due to Name-Based Virtual hosting, which is a method for hosting multIple domain names (with separate handling of each name) on a single server.
The /etc/hosts file is used to resolve a hostname into an IP address so we’ll need to add an entry in the /etc/hosts file for this domain to enable the browser to resolve the address for unika.htb. We do this using echo "{target IP} unika.htb" | sudo tee -a /etc/hosts, where | (pipe) sends the output of the echo command into the next command, tee -a /etc/hosts appends the input it receives into the file /etc/hosts (append adds to very end, doesn’t delete past data). So, it essentially maps the hostname unika.htb to the target Ip.

Now we can access the web page. After looking around, we find that we can change the language of the site and the url changes to the image below using the page parameter, which may be vulnerable to a local file inclusion vulnerability (LFI). LFI occurs when an attacker can get a website to include a file that was not intended to be an option for this application.

To test the page parameter to see if we can include files on the target system in the server response we search for the string below, where ../ is used to go back a directory, and multiple allow us to traverse back to C:\, and windows/system32/drivers/etc/hosts is one of the most common files that a penetration tester might attempt to access on a Windows machine to verify LFI is the hosts file.

This search tells us that LFI is possible as we can view the contents of the C:\windows\system32\drivers\etc\hosts file in the response. Next, we’ll try to capture the NetNTLMv2 of a user on the web server using Responder.
A NetNTLMv2 challenge / response is a string specifically formatted to include the challenge and response. This is often referred to as the NetNTLMv2 hash, but it's not actually a hash. Still, it is regularly referred to as a hash because we attack it in the same manner. A hash is a one-way function that takes any amount of data and returns a fixed size value, usually used to securely store passwords as there’s no way to convert it back to its original form. But we can compare the hash/ NetNTLMv2 of common passwords to the hash/ NetNTLMv2 we capture using a tool called John the ripper.
Responder is essentially a malicious SMB server we set up that when the target machine attempts to perform the NTLM authentication to that server, Responder sends a challenge back for the server to encrypt with the user's password. When the server responds, Responder will use the challenge and the encrypted response to generate the NetNTLMv2.
First, we’ll download Responder using the command in the image below.

Then we’ll cat Responder.conf to ensure that it is set to listen for SMB requests

Next, we’ll run sudo python3 Responder.py -I tun0, where python 3 is used to specify to run the Responder.py script using python3, and -I tun0 specifies to bind to and monitor traffic on the VPN tunnel interface tun0 rather than the machine’s physical NIC (network interface card)

While Responder is listening, we’ll search the string below using our attacking machine’s IP, and whatever where the web server tries to load this resource from our SMB server.

We’ll get an error but looking at responder, we see we’ve captured the NetNTLMv2 of the Administrator user.

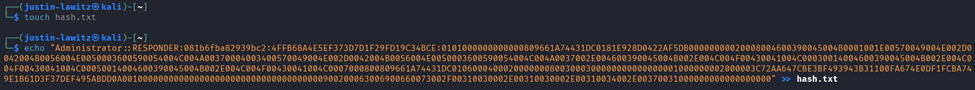
Then we’ll make a file using touch to hold this NetNTLMv2 and put the string into the file using echo “string” >> file to use it in John the ripper.
To run the NetNTLMv2 through john, we use john -w=WordListPath hash.txt, where -w= specifies the wordlist and hash.txt is the file we want to compare the hashes to. Running this command, we find the password badminton.

We'll connect to the WinRM service on the target and try to get a session. Because PowerShell isn't installed on Linux by default, we'll use a tool called Evil-WinRM which is made for this kind of scenario. -I specifies the target Ip, -u the username we discovered, and -p the password we cracked.

We can then search around and navigate out of the admin user using cd .. and enter the desktop of the user mike where we find the flag.txt file. We can finally use type flag.txt to read the file and capture the flag.



Comments